Sponsored by ForgeRock
Sponsored by Mandiant
Protecting Against Destructive Attacks: A Proactive Guide
Sponsored by CyberArk
Buyer's Guide to Managing Endpoint Privileges
Sponsored by Rockwell Automation
Self-Assessment: Cybersecurity Preparedness in Critical Infrastructure
Sponsored by Rockwell Automation
Report: Cybersecurity Preparedness in Critical Infrastructure
Sponsored by Rockwell Automation
The Comprehensive Resource Guide for Securing Critical Infrastructure
Sponsored by IBM
6 Myths of SIEM
Sponsored by Gigamon
Ransomware Resilience & Threat Trends: Learning from History and Martial Arts
Sponsored by Gigamon
Best Practices to Maximize Application Intelligence
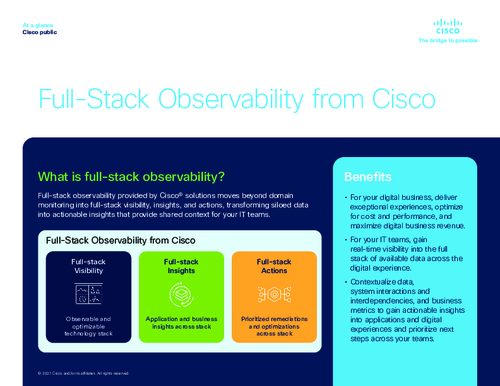
Sponsored by Cisco
Guide: How to Get Full Visibility Across Your Infrastructure
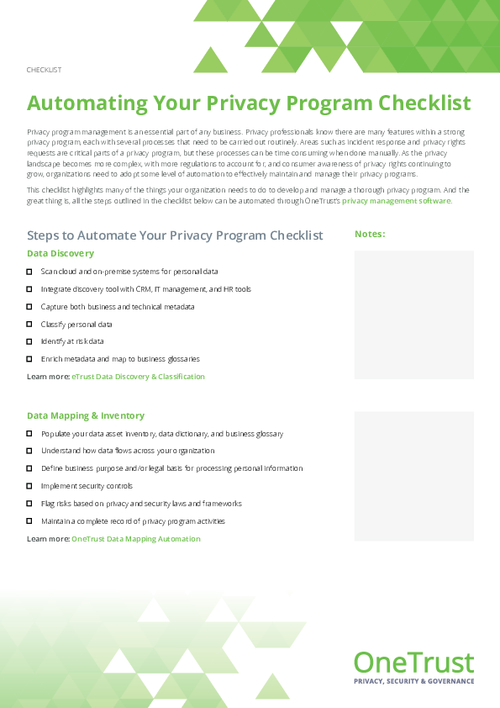
Sponsored by OneTrust