Sponsored by Synopsys
Sponsored by Synopsys
The CISO's Terrible, Horrible, No Good, Very Bad Day
Sponsored by Synopsys
The CISO's Ultimate Guide to Securing Applications
Sponsored by Splunk
5 Myths of AI & Machine Learning Debunked
Sponsored by Splunk
Modernise Your IT Monitoring with Predictive Analytics
Sponsored by Splunk
The SIEM Buyer's Guide
Sponsored by Splunk
Harden Your Defenses with SIEM Technology
Sponsored by Splunk
One Phish, Two Phish, Three Phish, Fraud Phish
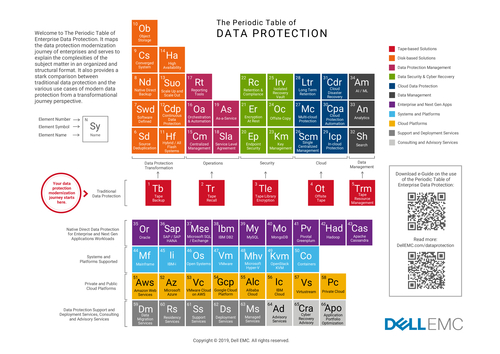
Sponsored by Dell EMC solutions with Intel
The Periodic Table of Data Protection
Sponsored by Dell EMC solutions with Intel
Data Protection Protect Your Data Capital From The Edge of the Core to the Cloud
Sponsored by iovation
The Evolution of Fraud in the Insurance Industry
Sponsored by OneTrust
Information Security Management System (ISMS) Industry Standards: A Help Guide
Sponsored by Splunk
The SIEM Buyer's Guide for Healthcare
Sponsored by Splunk