Sponsored by HCL
Sponsored by HCL
Embrace the Development and Security Powers of IAST
Sponsored by HCL
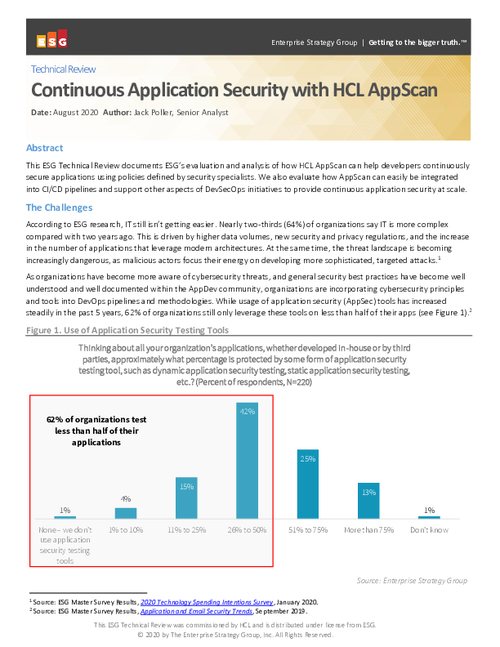
Maximize Your AppSec Program with Continuous Security
Sponsored by Radware
Securing Cloud-Native Kubernetes Applications
Sponsored by Radware
How to Keep APIs Secure from Bot Cyberattacks
Sponsored by Radware
The Top 9 DDoS Threats You Must be Prepared For
Sponsored by Radware
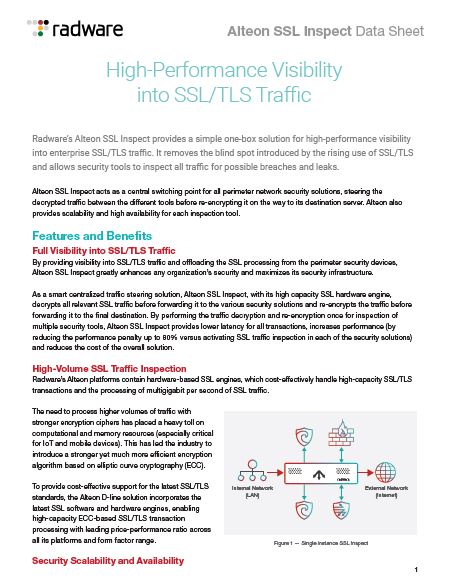
High-Performance Visibility into SSL/TLS Traffic
Sponsored by Okta
The Cost of Privacy Report 2020
Sponsored by Okta
Modernize Your Tech Stack Starting with Identity
Sponsored by Okta
Rethinking Reliance on Active Directory
Sponsored by Rapid7
The Four Pillars of Modern Vulnerability Management (French Language)
Sponsored by Rapid7
SIEM Solutions Buyer's Guide (French Language)
Sponsored by VMware