Sponsored by Harland Clarke
Sponsored by HyTrust
Take Inventory of Your Medical Device Security Risks
Sponsored by Bomgar
How to Solve 5 Privileged Access Problems
Sponsored by Tata Communicatiions
The State of Organizations' Security Posture as of Q1 2018
Sponsored by Zscaler
Modernizing Malware Security with Cloud Sandboxing in the Public Sector
Sponsored by Zscaler
Ransomware Costing Organizations Billions as CIO's and CISO's Lose Their Jobs
Sponsored by VMware and Intel
5 Areas for Rethinking IT Security
Sponsored by VMware and Intel
Protecting Data, Improving Agility, and Staying Compliant in the Mobile Cloud Era
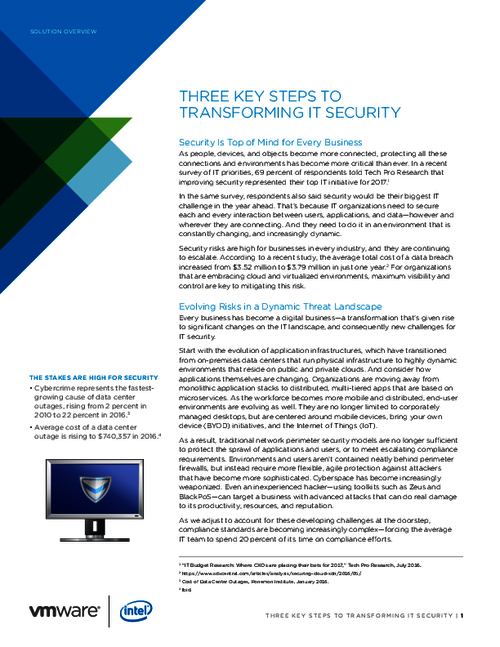
Sponsored by VMware and Intel
Three Essential Steps That Will Transform Your IT Security
Sponsored by IBM
Ransomware Response: Incident Lifecycle
Sponsored by IBM
Hybrid IT Security: Challenge Vs Triumph
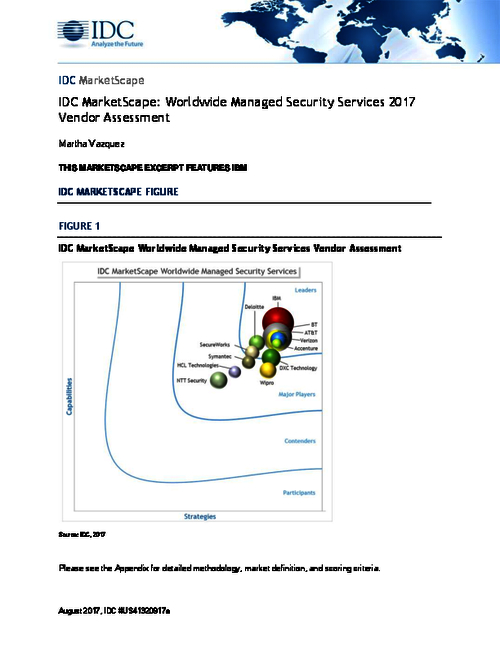
Sponsored by IBM
Assessing the Worldwide Managed Security Services
Sponsored by LogRhythm
Gartner Magic Quadrant SIEM Report
Sponsored by LogRhythm
How to Build a SOC with Limited Resources
Sponsored by NICE Actimize