Sponsored by Lastline
Sponsored by VMware and Intel
Guide to Rethinking Your IT Security
Sponsored by VMware and Intel
Transforming Security in the Mobile Cloud Era
Sponsored by VMware and Intel
3 Key Steps to Transforming IT Security
Sponsored by Zapproved
Shore Up Social Media and Digital App Security
Sponsored by Kaspersky Lab
Forward Facing Fraud Prevention
Sponsored by IBM
Why Phishing is so Appealing to Attackers
Sponsored by LogRhythm
Forrester Wave: Security Analytics Platforms, Q1 2017
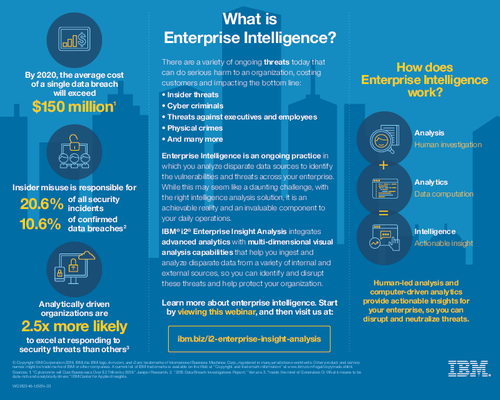
Sponsored by IBM
What is Enterprise Intelligence?
Sponsored by IBM
Know Your Attackers: Who Is Behind Cyberthreats?
Sponsored by IBM
Getting Ahead of the Fraud and Malware Threat
Sponsored by LogRhythm
Seven Ways to Simplify Public Sector Security Intelligence
Sponsored by Forcepoint