Sponsored by IBM
Sponsored by IBM
IBM X-Force Threat Intelligence Quarterly - 3Q 2015
Sponsored by Sophos
Endpoint Protection Buyers Guide
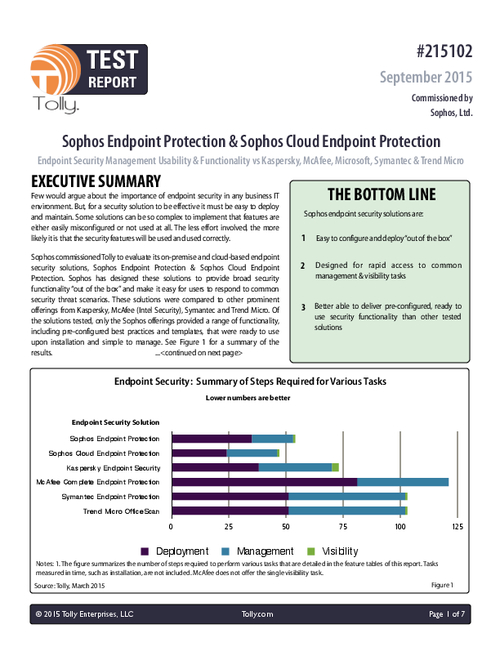
Sponsored by Sophos
Tolly Comparative Test Results: Endpoint Protection
Sponsored by Sophos
Deciphering the Code: A Simple Guide to Encryption
Sponsored by Sophos
Forrester Wave Report: Endpoint Encryption
Sponsored by Sophos
Encryption Buyers Guide
Sponsored by KnowBe4
The Phishing Breakthrough Point
Sponsored by KnowBe4
Ransomware: Hostage Rescue Manual
Sponsored by KnowBe4
How to Transform Employee Worst Practices Into Enterprise Best Practices
Sponsored by Spirent
Pentesting: The Required Human Ingenuity to Uncover Security Gaps
Sponsored by Spirent
How Strong is Your Malware Testing?
Sponsored by Fortscale
Eliminate Insider Threats with Precision and Speed
Sponsored by Fortscale
Case Study: Uncovering User-Based Insider Threats with Machine-Learning Algorithms
Sponsored by Fortscale