Sponsored by Imperva
Sponsored by Imperva
Global DDoS Threat Landscape
Sponsored by HCL Software
5 Steps to Alleviate Endpoint Management Tool Sprawl
Sponsored by HCL Software
Ensure Your Work from Home Endpoint Fleet is Secure and Compliant
Sponsored by HCL Software
Selecting an Endpoint Compliance Solution to Improve Your Security Posture
Sponsored by WatchGuard
Know Your Security Model: Traditional vs Contextual Protection
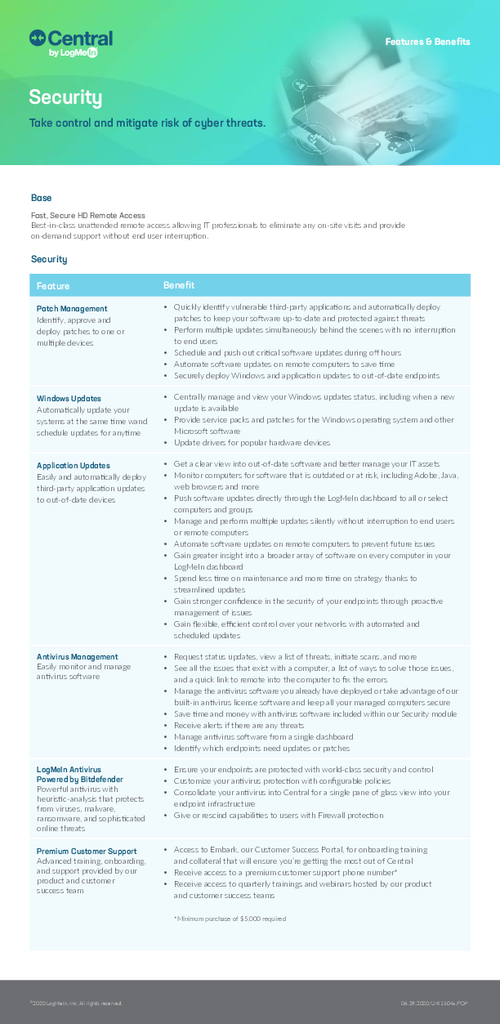
Sponsored by LogMeIn
Central Security Module Overview
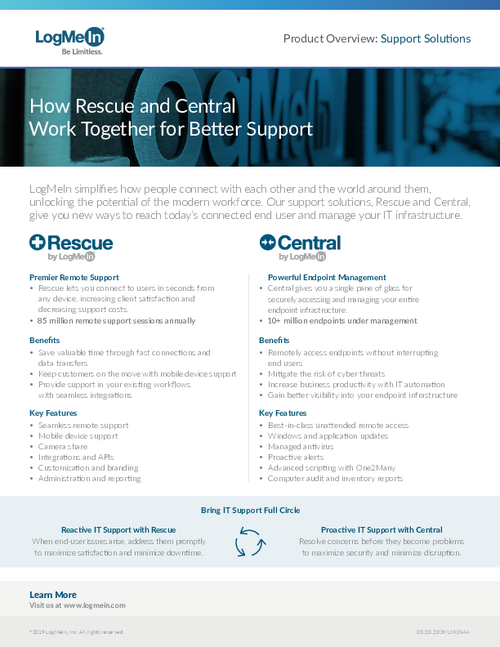
Sponsored by LogMeIn
How Central and Rescue Work Together for Better Support
Sponsored by McAfee
The Future of Network Security Is in the Cloud
Sponsored by McAfee
Enterprise Supernova: The data dispersion Cloud Adoption and Risk Report
Sponsored by McAfee
MVISION Unified Cloud Edge
Sponsored by Splunk
The Essential Guide to Data
Sponsored by HCL
Embrace the Development and Security Powers of IAST
Sponsored by Radware
How to Keep APIs Secure from Bot Cyberattacks
Sponsored by Sysdig