Sponsored by Central by LogMeIn
Sponsored by Auth0
Fixing Broken Authentication
Sponsored by Security Compass
What's the Real Cost of a Data Breach?
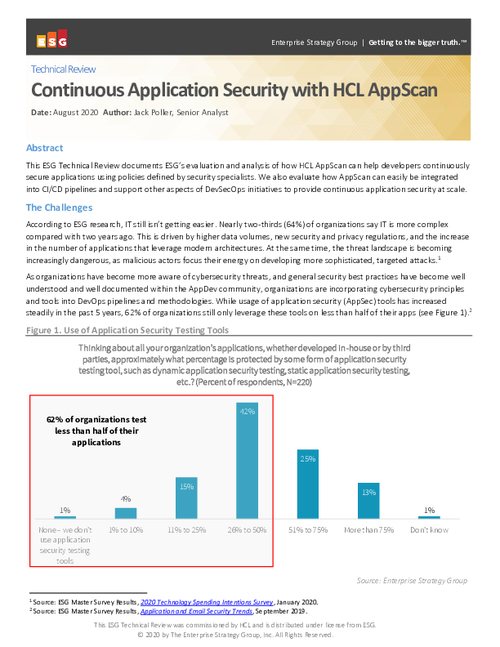
Sponsored by HCL
ESG: Continuous Application Security with HCL AppScan
Sponsored by HCL
Embrace the Development and Security Powers of IAST
Sponsored by Radware
Securing Cloud-Native Kubernetes Applications
Sponsored by Sysdig
IDC Guide: Evaluating Container Security Tools
Sponsored by Sysdig
NIST 800-190 Application Security Guide
Sponsored by Sysdig
Pike13 Case Study: Sysdig on Amazon ECS
Sponsored by Splunk
Gartner Magic Quadrant for APM
Sponsored by Synopsys
Modern Application Development Security
Sponsored by VMware