Critical Infrastructure Security , Cybercrime , Forensics
Senators Push for Action on Water Treatment Hack Investigation
Warner, Rubio Say Incident Raises Broader Security Issues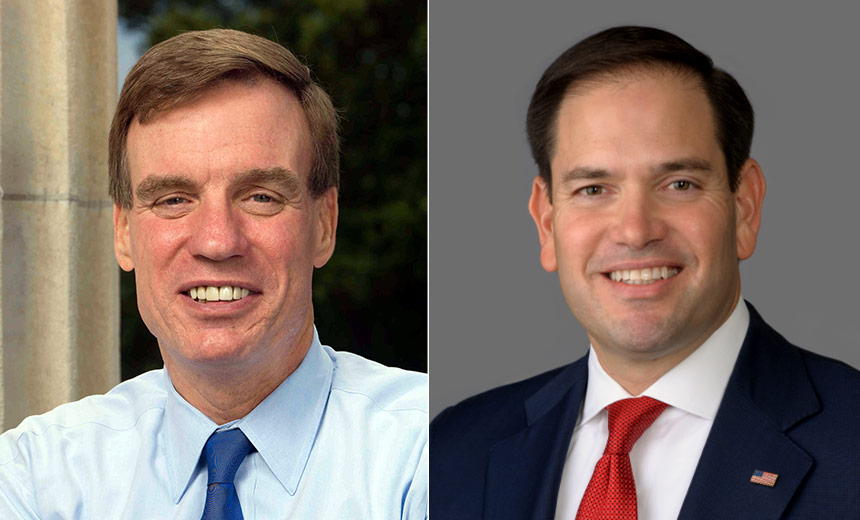
Sen. Mark Warner, D-Va., is demanding more information from the FBI and the U.S. Environmental Protection Agency about the Feb. 5 hacking of a water treatment facility in Oldsmar, Florida.
See Also: Cybersecurity for the SMB: Steps to Improve Defenses on a Smaller Scale
Meanwhile, U.S. Sen. Marco Rubio, R-Fla., has requested that the FBI provide "all assistance necessary" for the investigation, calling the incident a national security issue.
I will be asking the @FBI to provide all assistance necessary in investigating an attempt to poison the water supply of a #Florida city.
— Marco Rubio (@marcorubio) February 8, 2021
This should be treated as a matter of national security.
https://t.co/XhGNLplNpr via @vice
In the aftermath of the Florida hacking incident, the Cybersecurity and Infrastructure Security Agency on Feb. 11 issued a warning to operators of other plants to be on the lookout for hackers who exploit remote access software and outdated operating systems.
Warner's Requests
In a letter released Wednesday, Warner, the chair of the Senate Intelligence Committee, notes that the Florida incident has raised broad cybersecurity concerns about the nation's critical infrastructure.
"This incident has implications beyond the 15,000-person town of Oldsmar," the Virginia senator writes. "While the Oldsmar water treatment facility incident was detected with sufficient time to mitigate serious risks to the citizens of Oldsmar, and appears to have been identified as the result of a diligent employee monitoring this facility's operations, future compromises of this nature may not be detected in time."
In the letter, Warner demands information on three specific aspects of the investigation.
He asks the FBI for an update on any details about the hack it has uncovered.
In addition, he asks the EPA if the Oldsmar water treatment facility was compliant with the most recent version of the Water and Wastewater Sector-Specific Plan, a framework for developing security and resilience plans for these types of plants that are considered critical infrastructure. The senator also asks the agency if the plan, which was last updated in 2015, needs revisions to address the types of cybersecurity concerns raised by the Florida incident.
Finally, he asks for confirmation that agencies are sharing threat intelligence about this incident with other water treatment facilities throughout the U.S. as well as other organizations that are considered part of the nation's critical infrastructure.
"Other critical infrastructure sectors, such as healthcare, emergency services, energy, food and agriculture and transportation systems, depend on the cyber resilience of water facilities," Warner notes.
A spokesperson for the FBI could not be immediately reached for comment about the letter. An EPA spokesperson says the agency received the letter and would respond.
Hacker Gained Remote Access
Officials in Oldsmar, Florida, say a hacker gained remote access to a system to increase the amount of lye in the city's water system, but the attack was immediately thwarted (see: 5 Critical Questions Raised by Water Treatment Facility Hack).
As part of the initial investigation, officials found that the facility's staff routinely used TeamViewer to remotely gain access to some systems.
Some computers at the Florida plant reportedly were network-connected to the supervisory control and data acquisition - aka SCADA - system and were running outdated 32-bit versions of Windows 7, which is no longer supported by Microsoft (see: Florida City's Water Hack: Poor IT Security Laid Bare).
More Questions
Investigators and lawmakers should be asking the EPA and other agencies even more questions, says Mike Hamilton, a former vice chair of the Department of Homeland Security's State, Local, Tribal, and Territorial Government Coordinating Council.
For example, he says the EPA should clarify whether it has established criteria and funding for cyber risk management at water treatment plants.
And he says the FBI and EPA should be pressed to determine if the hacker who targeted the Florida plant exploited a specific vulnerability or just gained access to system credentials.
"The investigation should seek to establish the taxonomic identity of the threat actor or actors, such as whether this was opportunistic, hacktivist, criminal or nation-state activity, as this will help to understand the motivation of the actors and the likelihood of further events," says Hamilton, who now serves as CISO of CI Security. "Secondarily, investigators should review the guidance provided by the EPA and other agencies as to security requirements and the extent to which those requirements span the information and operational technology demarcation point."
Austin Berglas, who was an assistant special agent in charge of cyber investigations at the FBI's New York office and is now the global head of professional services at cybersecurity firm BlueVoyant, says the FBI is likely investigating the incident from two separate angles.
"The FBI’s focus for this investigation will be to first, ensure that the incident is contained and there is no ongoing threat to the water treatment plant," Berglas says. "Second, the FBI will attempt to attribute the attack to a specific group or individual through analysis of indicators of compromise and the tactics, techniques, and procedures used by the attacker."